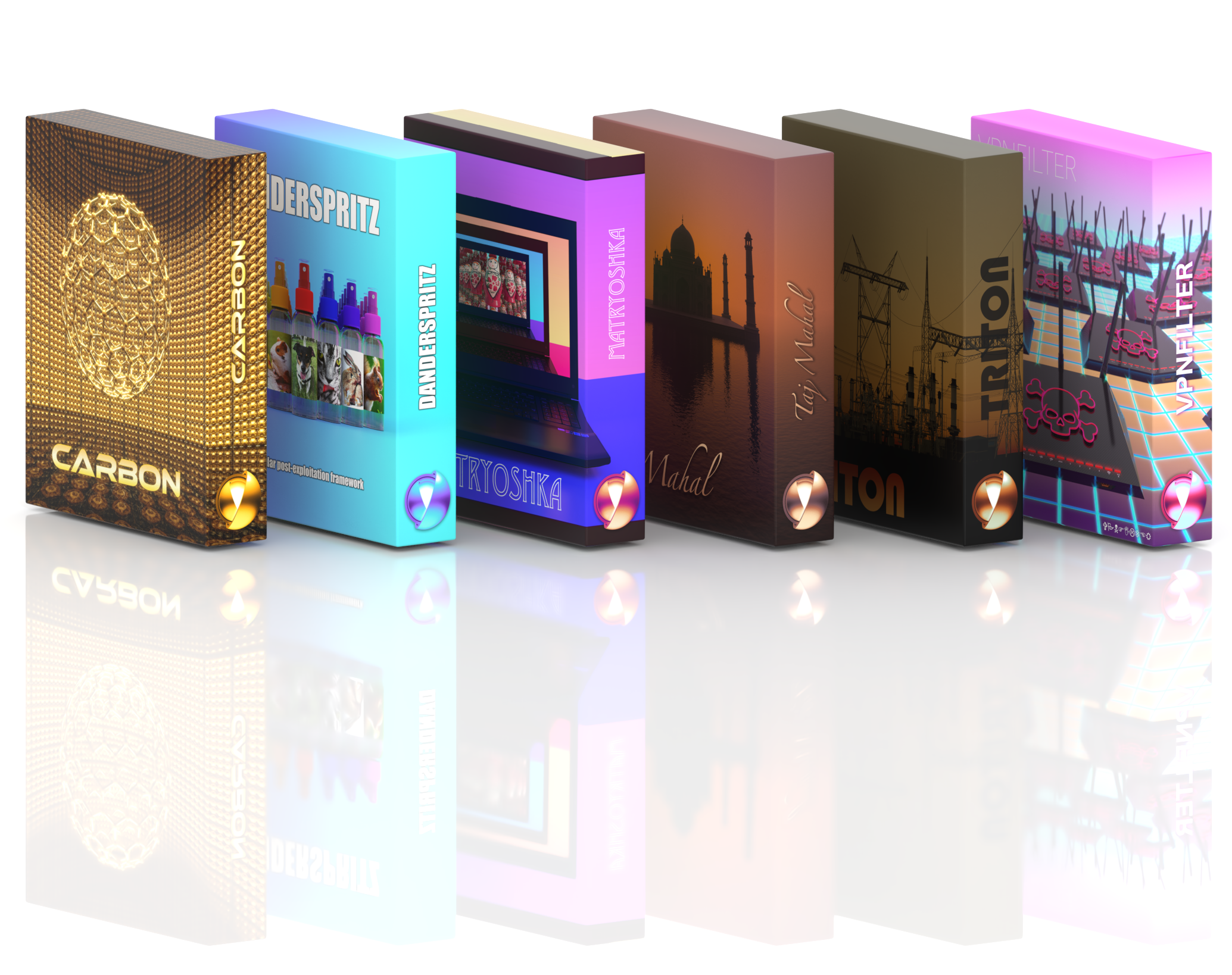
The first of what promises to be an ongoing series of volume releases of nation state sponsored hacking tools. The Advanced Persistent Threat Collection Volume 1 highlights a handful of advanced attack frameworks, taking malware to a whole new level. What all of these malware packages have in common are the following elite features:
Malware is downloaded in multiple stages
An initial attack downloads an implant that reaches out to a remote command and control server.
Once contact is established, second-stage malware is downloaded and installed on the compromised system.
A collection of custom modules are loaded and executed on the target via a remote application controlled by mission ops.
Software is customized using a mixture of in-house and open source tools
Targeting is highly selective